Installing or Renewing a 2048 bit SSL Certificate on Citrix Access Essentials/Xenapp Fundamentals
June 29, 2012 15 Comments
I had to renew a 2048 bit Godaddy SSL certificate on a Citrix Access Essentials server today. This article on the Citrix knowledgebase explains how to install the certificate in Quick Start, but is a bit light on detail for the IIS part so I thought I would document it here.
Firstly you need to generate a certificate request or renewal request on the Citrix Access Essentials or Xenapp Fundamentals external website in IIS manager. Right click the website and choose ‘properties’, then click on the ‘Directory Security’ tab. In the ‘Secure Communications’ section click on the ‘Server Certificate’ button, and the server certificate wizard will start. Click Next, and the following screen will appear:
In this case I was renewing the existing 2048 bit certificate, so selected ‘renew the current certificate’ and clicked next. On the next screen choose ‘prepare the request now but send it later:
Finish the wizard, and save the request for processing with your SSL provider. In this case the provider is Godaddy, but the process will be similar for other providers. Log into Godaddy, select the certificate you want to renew (assuming you have already purchased the renewal credit), and choose ‘Request Certificate’ .
On the next screen select ‘Third Party or Dedicated Server, and then paste the contents of the certificate request that you generated in IIS into the CSR field as shown:
Submit the request and then wait for Godaddy to process it, completing any necessary domain control, or other validation processes that may be required. Once the certificate processing is complete, download your new certificate from Godaddy. If this is the first time you have installed a Godaddy certificate on the server you will also need to install intermediate certificates that come in the zip file on your server. Further documentation on this can be found on the Godaddy website here.
Next install the new certificate using IIS manager. Again, right click the Citrix external website and choose ‘Properties’, then click on the ‘Directory Security’ tab. In the ‘Secure Communications’ section click on the ‘Server Certificate’. In the wizard choose ‘process the pending request and install the certificate’.
Browse to the new certificate .crt file you downloaded from Godaddy and click next. You may need to select ‘All files’ to view this file.
Now the next screen can cause a bit of a gotcha. By default the wizard wants to choose standard SSL port 443 to install this certificate on. If you select this port it will conflict with Citrix and cause an error message when accessing the website after installing the certificate. Make sure you select a different port in the wizard, such as 444 to prevent a conflict with Citrix Access Essenstials, then click ‘Next’.
Failure to change the port will result in the error ‘Bad Gateway! The proxy server received an invalid response from the upstream server. Error 502’, which can be seen below:
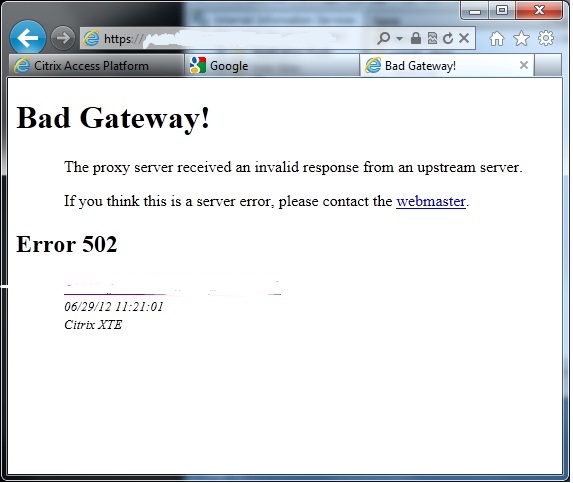
Error message when installing new SSL certificate on Citrix Access Essentials/Xenapp Fundamentals Bad Gateway error 502
Review the final screen, and complete the wizard. Finally, run up the Citrix quick start tool and choose ‘Manage External Access’, under the ‘External Access’ section. From here you can choose the new certificate to use with Citrix Access Essentials. These steps are documented in the Citrix document. After that you’re done!






