Apply a Group Policy to a Specific Operating System
October 25, 2011 Leave a comment
During our Windows 7 rollout it was necessary to apply some specific registry settings to the new Windows 7 machines without affecting the legacy Windows XP clients. This can easily be done by creating a WMI filter in the Group Policy Management Console and applying it to the relevant GPO.
To do this simply fire up gpmc.msc and click on the ‘WMI Filters’ section under the domain you want to create the group policy object (GPO) in.
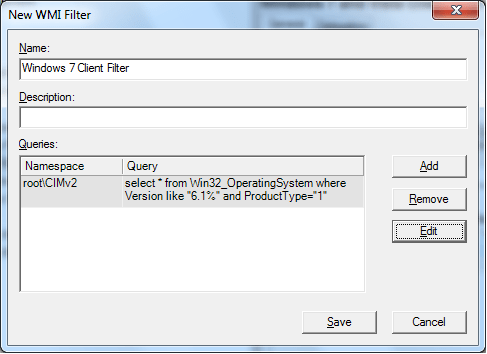
Right click the ‘WMI Filters’ section and choose ‘New’. Give the filter a name. Click on ‘Add’ and type the following to create a filter for Windows 7:
select * from Win32_OperatingSystem where Version like “6.1%” and ProductType=”1″
Finally, you need to apply this filter to the GPO that you want to use. In this example a GPO called ‘Windows 7 GPO’ has been created. Highlight the GPO in the Group Policy Management Console, and then under the ‘Scope’ tab, apply the WMI filter you created, by selecting it from the drop down list in the ‘WMI Filtering’ section as shown below:
You can filter the following operating systems in this way by adjusting the query in the WMI filter. Operating systems can be defined as follows:
Windows XP:
select * from Win32_OperatingSystem where (Version like “5.1%” or Version like “5.2%”) and ProductType = “1”
Windows Vista:
select * from Win32_OperatingSystem where Version like “6.0%” and ProductType = “1”
Windows 7:
select * from Win32_OperatingSystem where Version like “6.1%” and ProductType = “1”
Windows Server 2003:
select * from Win32_OperatingSystem where Version like “5.2%” and ProductType = “3”
Windows Server 2008:
select * from Win32_OperatingSystem where Version like “6.0%” and ProductType = “3”
Windows Server 2008 R2
select * from Win32_OperatingSystem where Version like “6.1%” and ProductType = “3”
You can use the ‘ProductType’ part of the query to specify whether the operating system is a client, server, or domain controller.
ProductType = “1” is a client
ProductType = “2” is a server operating as a domain controller
ProductType = “3” is a member server. i.e. not operating as a domain controller